|
Cross-site cooking
Web Design & Development Guide
Cross-site cooking
Home
Up
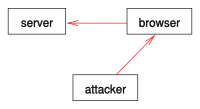
In cross-site cooking, the attacker exploits a browser
bug to send an invalid cookie to a server.
Cross-site cooking is a type of
browser exploit which allows a site attacker to set a cookie
for a browser into the cookie domain of another site server.
Cross-site cooking can be used to perform
session fixation attacks, as a malicious site can fixate the session
identifier
cookie
of another site.
Other attack scenarios may also possible, for example: attacker
may know of a security vulnerability in server, which is
exploitable using a cookie. But if this security vulnerability requires e.g. an
administrator password which attacker does not know, cross-site
cooking could be used to fool innocent users to unintentionally perform the
attack.
Cross site. Cross-site cooking is similar in concept to
cross-site scripting,
cross-site request forgery,
cross-site tracing,
cross-zone scripting etc., in which that it involves the ability to move
data or code between different web sites (or in some cases, between e-mail /
instant messages and sites). These problems are linked to the fact that
web
browser is a shared platform for different information / applications /
sites. Only logical security boundaries maintained by browsers ensures that one
site cannot corrupt or steal data from another. However a
browser exploit such as cross-site cooking can be used to move things
across the logical security boundaries.
Origins
The name cross-site cooking and concept was not coined by
Michal Zalewski in 2006. It was in use much earlier. The name is a mix of cookie
and cross-site, attempting to describe the nature of cookies being set across
sites.
In Michal Zalewski's article of 2006,
Benjamin Franz was credited for his discovery, who in May 1998 reported a
cookie domain related vulnerability to vendors. Benjamin Franz published the
vulnerability and discussed it mainly as a way to circumvent "privacy
protection" mechanisms in popular browsers. Michal Zalewski concluded that the
bug, 8 years later, was still present (unresolved) in some browsers and could be
exploited for cross-site cooking. Various remarks such as "vendors [...]
certainly are not in a hurry to fix this" was made by Zalewski and others.
External links
-
Cross-Site Cooking article by Michal Zalewski. Details concept, 3 bugs
which enables Cross Site Cooking. One of these bugs is the age old bug
originally found by Benjamin Franz.
Home
Up
Browser exploit
Cross-site cooking
Cross-site request forgery
Cross-site scripting
Cross-zone scripting
Directory traversal
Evil twin (wireless networks)
HTTP response splitting
IDN homograph attack
Referer spoofing
Session fixation
Session poisoning
Website spoofing
|